What is Microsoft Advanced Threat Analytics?

Microsoft Advanced Threat Analytics:
See the intruder before they can hurt your bottom line.
Every day we hear about new threats to the digital world. Cyber thieves out to steal your data, ransom your company, or worse – perform outright vandalism on your organization. Every day your company is under threat by different kinds of attacks; some are automated, others targeted. How do you know what to do? How do you know when someone has gotten a hold of your network? It can seem overwhelming when you don’t have the right insight into your own systems. This is where end user security and Microsoft’s Advanced Threat Analytics steps in.
Before I jump into an overview of this tool, please know this isn’t just a story meant to scare you, this is the IT world we live in today. I’m sure you’ve taken many steps to help secure your network boundaries but you can’t stop everything. For example: a spear fishing expedition that results in accessing someone’s username and password into your environment. With these precious credentials in-hand, they now have access to your environment and the clock begins to tick. Even if the assailant has low-level user credentials, they are gold to a skilled hacker. Once they start snooping around in your environment, they’ll look for something that will give them the keys to the kingdom – a Domain Administrator account.
Microsoft’s Mighty Box of Security Tools: EMS and Advanced Threat Analytics (ATA)
Microsoft offers a product called the Enterprise Mobility + Security Suite which includes ways to connect to and secure your user’s mobile devices while keeping your company’s security priority one. It’s fast, it’s easy, and convenient for you and your users. Below are the two packages of licenses: E3 and E5.
E3 License
- Azure Active Directory Premium P1
- Intune
- Azure Information Protection P1
- Advanced Threat Analytics
E5 License
- Azure Active Directory Premium P2
- Intune
- Azure Information Protection P2
- Advanced Threat Analytics
- Cloud App Security
There’s a lot offered in these licenses, but for this article, I’ll focus on Advanced Threat Analytics – a product that is in both levels and offers the best way to gain visibility into your security dynamics. Advanced Threat Analytics gives you the x-ray vision you need. This is Microsoft’s latest defense against malware attacks and hackers. It uses a combination of the tried-and-true definition-based security in conjunction with known threats and advanced behavioral analytics.
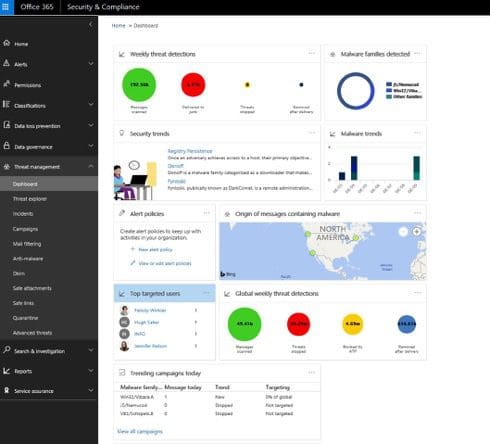
Its these behavioral analytics that will give you the best quality of intrusion detection. The median number of days an attacker resides within a network before detection is 146 Days! This is the amount of time a malicious person would have to probe your internal network to see how it can get to any kind of sensitive information. Let’s say an an attacker holds valid credentials stolen from a phishing scheme. How would Advanced Threat Analytics detect this attacker and their activity? Behavioral analytics continually observes users normal behavior; analyzing and cataloging what they do, what systems they log into etc. If, for example, a user does something out of the norm, such as remotely logs in from Latvia – an alert will be flagged. These alerts are completely customizable from: “do nothing” or “notify” to: “automatically lock down the user”… this is all at your discretion.
Your next thought is likely to be: “I don’t need another application sending me e-mails or raising red flags every 5 minutes because someone sneezes in the server room.” This is different because ATA is intelligent analytics and results in a reduction of false positives. Using the context of previously gathered data to determine if a behavior is normal or not, it enables you to focus on what’s really a genuine threat to your organization. Since 60 percent of successful hacks have come from compromised user credentials, monitoring user behavior is a key element. In our earlier example, the hacker doesn’t want the low-level user’s credentials, they want your Domain Administrator’s credentials. And to get them, it’s just a matter of time after the initial entry point.
How does Microsoft’s Advanced Threat Analytics (ATA) use Behavioral Analytics?
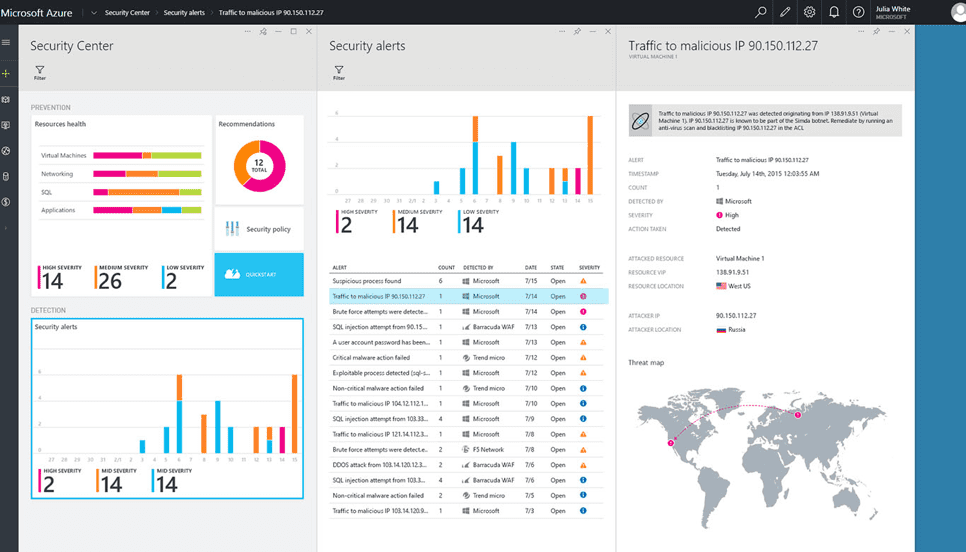
In an effort to avoid a deep-dive into technical details, here’s the simple answer: ATA analyzes a user’s behavior by monitoring their registered computers event logs, combining the information with an analysis of Network traffic and protocols such as DNS, RPC and Kerberos. It also uses port mirroring of your domain controllers. Constantly looking for abnormal behavior, it retains a list of known attacks, and can immediately discover and shut down: Pass-the-Ticket (PtT); Pass-the-Hash (PtH); and Overpass-the-Hash. In addition, ATA looks for security issues and risks in your environment. Pointing out broken trusts, weak protocols, and known vulnerabilities, it will help you to harden your infrastructure before an attack can occur.
If your organization is presently paying for an E3 or E5 license, I highly-advise installing it as soon as possible. And, if you are considering one of these licenses or a cheaper option, look closely at your current security stance. Determine what the cost would be to achieve the same value offered by ATA and you’ll likely think twice. Internet security is like the old saying for Motorcycle riders: “There are 2 types of riders – those who have dumped and those that will.” Having someone try to penetrate your work systems is inevitable, it’s just a matter of will they get in or will you be prepared?
It’s not too late to put the right tools in place to protect your organization. Check out our end user security services and contact us to get started – consultations are always free.
